A Venture Capital Company Modernizes its Security Posture by Migrating from Okta to Microsoft Entra ID
The company modernized its security by migrating from Okta to Microsoft Entra ID, streamlining identity management and application access with enhanced MFA, all achieved with minimal disruption.

Challenges
The customer was faced with the following challenges:
- Migrate a large portfolio of enterprise and SaaS applications from Okta to Microsoft Entra ID while minimizing business disruption.
- Recreate SSO and user lifecycle management (provisioning/deprovisioning) for diverse application patterns.
- Address an application-specific provisioning gap where Entra ID could not match Okta’s provisioning behavior without customization.
- Improve security posture by enabling modern MFA and aligning sign-in controls with updated access policies.
Solution
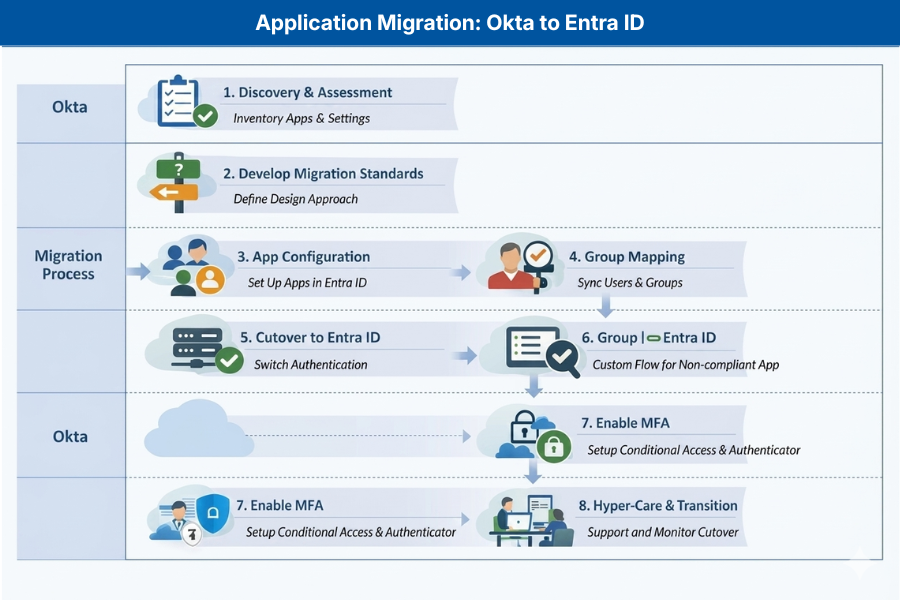
Netwoven employed a phased approach to plan, execute, and stabilize the Okta to Entra ID migration. The engagement leveraged repeatable migration patterns, wave-based cutovers, coordinated testing, and structured hyper-care. In parallel, we enabled MFA and aligned sign-in protections using Conditional Access to improve overall security posture.
| Phase | Objective | Approach | Outcome |
| Workshops and Requirements Finalization | Confirm scope, application inventory, and target-state requirements | Conduct workshops with stakeholders to validate application catalog, SSO methods, provisioning needs, dependencies, and cutover constraints; define migration waves and success criteria. | Approved migration backlog and wave plan with agreed acceptance criteria. |
| Migration Standards and Design | Create repeatable patterns to accelerate migrations | Define standards for enterprise application configuration, claims and attribute mapping, SAML/OIDC configuration, Conditional Access baselines, and provisioning patterns. | Documented playbooks and standards to ensure consistent configuration and faster execution. |
| Build and Migration Execution | Migrate applications with controlled testing and cutovers | Configure Microsoft Entra enterprise applications, replicate SSO settings from Okta, validate access with application owners, coordinate cutovers, and track progress by wave. | 270 applications migrated from Okta to Entra ID with validated access. |
| Provisioning Exception Handling | Maintain continuity for a provisioning-dependent application | For one application where Entra ID provisioning could not replicate Okta’s provisioning behavior, implement a coexistence approach: keep the application on Okta temporarily while designing a custom workflow to achieve the required provisioning outcomes. | Business continuity maintained; roadmap established for custom workflow and eventual transition off Okta for that application. |
| MFA Enablement | Strengthen authentication and reduce sign-in risk | Enable MFA using Microsoft Authenticator and implement policy-based sign-in controls using Conditional Access; pilot, refine, and expand to production rollout. | Modern MFA enabled and aligned sign-in protections established. |
| Hyper-care and Transition | Stabilize the environment post-migration | Provide post-cutover monitoring, rapid issue remediation, knowledge transfer, and operational runbooks for steady-state operations. | Smooth transition to steady-state operations with reduced IAM overhead. |
Benefits
This Okta to Entra ID modernization achieved a few key business benefits.
- Platform Consolidation: Centralized identity and access management on Microsoft Entra ID to simplify administration and reduce tool sprawl.
- Cost Savings: The migration delivered measurable cost savings by decommissioning Okta licenses for users without Okta‑dependent applications, leveraging Microsoft Entra ID capabilities already included in the organization’s Microsoft 365 licensing.
- Stronger Security: Improved security posture through MFA enablement and policy-based access controls.
- Low-Risk Transition: Reduced migration risk with repeatable patterns, wave planning, coordinated testing, and structured hyper-care.
- Business Continuity: Clear remediation path for exceptional provisioning scenarios without impacting business operations.