Govern who — and what — acts in your environment.
Modernize identity, eliminate access risk, and enable secure work — without slowing your business.
First-class identity for AI agents. Modernized Entra ID for humans. Conditional Access that extends across both. Microsoft Entra-native, including the new Microsoft Entra Agent ID and Microsoft Agent 365 control plane.

Why Identity & Access Management Is Harder Than It Looks
As identities multiply across users, apps, clouds, and devices, traditional IAM approaches fail to keep up — creating security gaps, compliance risk, and operational complexity.
Services
According to a Forrester study, implementing Microsoft Entra and replacing legacy infrastructure delivers a 240% ROI, significantly reducing costs and effort while driving substantial productivity gains.
Entra ID Implementation & Migration
Migrate from legacy identity systems (e.g., Okta, AD) to Microsoft Entra ID for cloud-native identity management, SSO, and Zero Trust readiness
Customer Identity & Access Management (CIAM)
Entra External ID enables secure, scalable access for customers and partners with social login, consent, and passwordless auth
Passwordless Authentication
Deploy passwordless authentication (FIDO2, Windows Hello) and streamline login flows to reduce friction, improve security, and cut helpdesk costs
Managed IAM Services
Outsourced identity operations including provisioning, policy management, and compliance support; 24/7 coverage and Entra ID administration
AI Agent Identity Management
Govern non-human identities like bots and ML models just like human accounts and other accounts that follow governance protocols
Identity Governance & Compliance
Implement access reviews, role-based access control, and privileged identity management to meet audit and regulatory requirements
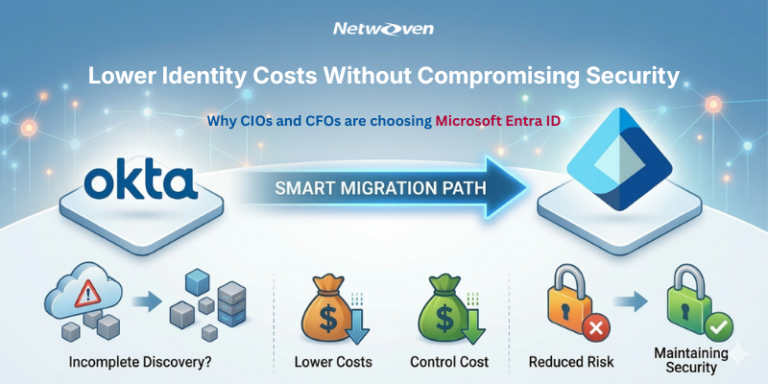
Okta to Entra ID Migration
Migrate from Okta to Microsoft Entra ID in as little as 60 days with a strategy that eliminates risk and ensures a seamless identity transition
Offers
Take the next step in securing your organization with Netwoven’s Identity and Access Management (IAM) solutions.
Our Methodology
A phased methodology to reduce risk, improve governance, and modernize identity at scale.
01
Discover & Score
Inventory human identities, service principals, and AI agents (Copilot Studio, Power Platform, custom-built). Assess Conditional Access posture, MFA coverage, privileged access risk, and orphaned access. Quantify against Microsoft baselines.
02
Design & Plan
Identity architecture aligned to Zero Trust. Agent identity blueprint design. Conditional Access policy design (human + agent). Roadmap prioritized by risk reduction.
03
Deploy & Configure
Microsoft Entra ID, Conditional Access, MFA, PIM, Identity Governance, and (where applicable) Microsoft Entra Agent ID — deployed to production standards.
04
Activate & Adopt
Train identity teams on new constructs. Roll out access reviews, joiner/mover/leaver workflows, agent identity provisioning. User communication and adoption tracking.
05
Detect & Respond
Operate the identity platform. Triage Conditional Access alerts. Tune policies based on real signal. Respond to identity-driven incidents.
06
Optimize & Mature
Continuous tuning, regulatory updates, posture improvement. Quarterly executive readouts on identity coverage, access review completion, agent governance, and incident trends.
Client Success Stories

Relay GSE Migrated from Okta to Entra ID
Relay GSE migrated from Okta to Entra ID and decreased maintenance and license costs significantly….

Global SaaS Firm Moves from Okta to Entra ID
A leading SaaS Company Moves from Okta to Entra ID to Streamline M365 and Reduce Costs…
The Netwoven Advantage
Most security firms come from the SOC. Most Microsoft partners don’t go deep on data. We’re built where they meet — and we have productized IP no other partner offers.
25 Years of M365 + Content Depth
Quarter-century of SharePoint, Teams, OneDrive, and Exchange. We know where your sensitive data actually lives.
5 Pillars – End-to-End Capability
Few partners credibly span AI data security, compliance, AI Agent identity, endpoint, SOC, and . We deliver across all five pillars.
Govern 365 – Productized IP
M365-native VDR-grade Microsoft Purview based secure collaboration product that no other Microsoft partner offers. Real product, not slideware.
Microsoft Alliance and Certifications
Active partnership, co-sell access, MAICPP funding eligible. Information Protection & Governance Specialization in pursuit.
FAQs
Microsoft Entra Agent ID is a purpose-built identity framework for AI agents within Microsoft Entra. As of 2026, it is in preview through Microsoft’s Frontier early-access program and is part of Microsoft Agent 365. Production rollouts are possible with appropriate scoping; full GA timing is determined by Microsoft. We support customers in Frontier-eligible environments.
Service principals were designed for long-lived services with known ownership and managed lifecycle. AI agents are dynamic — sometimes created and destroyed thousands of times per day with no fixed owner. Borrowing service principals creates orphaned credentials, audit blind spots, and access decisions made by the wrong principal. Entra Agent ID solves this by giving each agent its own identity construct.
Microsoft Agent 365 is the unified control plane for observing, securing, and governing AI agents at enterprise scale. Microsoft Entra Agent ID is the identity layer within Agent 365. Together they provide identity assignment, lifecycle management, Conditional Access for agents, and centralized visibility across both Microsoft and third-party agents.
Yes. When Copilot Studio creates an agent in environments with Entra Agent ID enabled, an agent identity blueprint and agent identity are automatically created. This means governance — ownership, access reviews, decommissioning — applies to Copilot Studio agents the same way it applies to other identities. Frontier-eligible customers can pilot this today.
Conditional Access policies extend to AI agents through Entra Agent ID, with adaptive controls that evaluate agent risk, behavioral signals, and context before granting access. Microsoft Managed Policies provide a baseline that blocks high-risk agents, with custom policies available for nuanced cases. Implementation patterns are still emerging as Agent ID matures from preview.
Human IAM assumes long-lived identities with credentials, MFA, and behavioral patterns. Agent IAM assumes ephemeral identities created dynamically, with no human credentials, federated authentication via blueprints, and behavioral patterns measured at machine scale. Both run on Microsoft Entra, but the security model and lifecycle differ meaningfully.
Microsoft Entra Agent ID requires Microsoft Entra ID as the identity platform. Organizations on Okta or other legacy IAM either need to migrate or run Entra alongside their existing platform for AI workloads specifically. Most enterprises find it cleaner to consolidate; Forrester reports 240% ROI on Entra modernization vs. legacy platforms.
Entra Agent ID extends Microsoft Entra ID Governance — the same access reviews, entitlement management, and lifecycle workflows you use for human users now extend to agent identities. This means audit reporting, segregation of duties, and joiner/mover/leaver discipline can be applied uniformly across humans and agents.
Phased: inventory current service principals being used as de-facto agent identities, classify by use case (long-lived service vs. dynamic agent), provision new agent identities for the dynamic cases, migrate access grants, decommission orphaned service principals. The Agent Identity Readiness Assessment maps this for your environment.
Tightly. AI Data Security (Pillar 1) controls what data AI agents can access; AI Agent Identity (Pillar 3) controls who or what is doing the accessing. Without Pillar 3, you can’t enforce least-privilege for agents. Without Pillar 1, even properly-identified agents can over-share. Most enterprises deploy them in sequence — Pillar 1 first, then Pillar 3.
Latest Insights
Cut Identity Costs Without Cutting Security: Why CIOs and CFOs Are Migrating from Okta to Microsoft Entra ID
5 Things to Expect from a Zero Trust Implementation Workshop
Start your digital transformation with confidence.
Whether you're planning a migration or optimizing your environment, our experts are here to help you move faster and more securely.
Prefer to call?
+1-877-638-9683Drop us a mail
info@netwoven.comSchedule a Capability Discovery Call
🔒 No spam. Your information stays private.