Introduction
Stop paying for identity. Start owning your security.
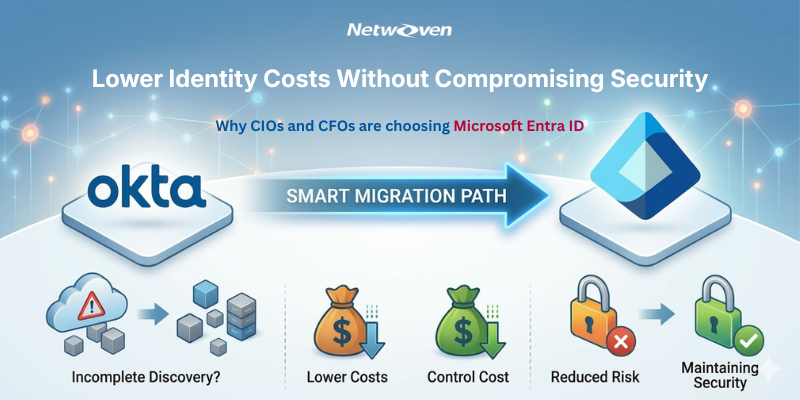
Feature parity between Okta and Microsoft Entra ID is no longer a debate. Organizations that consolidate on Entra ID gain more than cost savings – they gain a deeply integrated identity security platform backed by Microsoft’s full threat intelligence suite, built-in Zero Trust controls, and a governance engine that automates the access lifecycle from hire to retire.
This is the real evaluation-stage problem. The decision isn’t “Okta vs Entra” in isolation. The decision is:
- Can we consolidate identity and remove redundant cost without compromising security?
- Can we do it with predictable scope, timeline, and risk?
- Can we prove the plan before committing to execution?
Proof of what credible scoping looks like
A real-world Okta to Entra ID migration program doesn’t start with guesswork. In one documented Netwoven migration program, scoping accounted for 300 users, 156 applications, and 66 Okta groups—exactly the kind of “messy reality” that causes scope creep when discovered late.
Why Okta to Entra ID migrations go over budget (and why it’s rarely “engineering difficulty”)
Most cost overruns aren’t because Microsoft Entra ID is hard. They happen because identity environments are not as clean as anyone believes until you try to move them.
1) The application inventory illusion
Every enterprise believes it has an “app list.” Then discovery begins and the long tail appears:
- Apps federated years ago with custom SAML quirks
- OIDC/OAuth apps with redirect URI sprawl
- Provisioning connectors and workflows nobody remembers owning
- “Temporary” integrations that became permanent
Each newly discovered app is not just a line item; it’s real work: configuration, claims, certificates, testing, and sign‑off. When discovery is incomplete, the plan is fiction.
For context on the messy, real-world issues that break plans, read this blog.
2) Identity edge cases show up late and become change orders
Okta environments accumulate years of edge-case logic that “just works” today:
- Joiner/mover/leaver behavior encoded in provisioning rules
- Contractor/partner identities with special handling
- Service accounts and automation paths that cannot tolerate surprises
- Groups that double as entitlement systems
When these are discovered mid‑project, teams decide under time pressure. That’s when scope expands.
3) Migration quietly turns into modernization (and CFOs pay for the blur)
Teams start with “migrate identity.” Then someone says:
- “While we’re here, let’s redesign Conditional Access.”
- “We should clean up groups and permissions too.”
- “Let’s modernize provisioning flows at the same time.”
These can be valuable initiatives but mixing them into a migration is how programs become unpredictable.
CFO rule of thumb: If modernization is happening, it must be explicitly costed and staged, not smuggled into migration scope.
The CFO + CIO decision frame: Cost, Risk, and Control (not features)
When CFOs and CIOs evaluate Okta to Entra ID migration (or Okta to Azure AD migration), the winning plan creates control in three areas.
A) Cost control
You can’t control how messy the environment is, but you can control when you discover it.
A credible plan gives you:
- A complete inventory of what exists (apps, groups, policies, flows)
- A boundary between migration and optional optimization
- A phased plan that limits blast radius
B) Risk control
Identity migration risk is operational:
- Users can’t sign in
- Apps fail SSO
- Provisioning breaks lifecycle hygiene
- Helpdesk volume spikes
- Security posture drifts due to emergency exceptions
A credible plan assumes friction and designs for safe change.
C) Control of outcomes
Outcome control is how CFOs trust the plan and CIOs defend the execution. Define what “success” means before the first cutover.
What Netwoven’s fixed‑price, fixed‑scope assessment actually produces (and why it changes the decision)
Many vendors sell confidence while Netwoven’s assessment produces artifacts you can fund and govern.
A fixed‑scope assessment is designed to answer the CFO’s and CIO’s real questions:
- What exactly are we migrating (and what are we not)?
- Where are the risk hotspots (apps, policies, provisioning, identifiers)?
- What is the phased execution sequence that keeps the business running?
- What is the cost optimization path once redundancy is removed?
Milestone deliverables (CFO-friendly specificity)
A credible Okta to Entra ID migration program is milestone-driven. Typical deliverables include:
| Milestones | Output |
| Okta discovery & analysis | Inventory including provisioning rules; migration strategy for apps and users |
| Entra ID readiness & health check | MFA/SSPR/Conditional Access posture findings and recommendations |
| Strategy & planning | Detailed project plan, application staging, test migration readout |
| Change management | Communications calendar, templates, FAQs, and enablement |
| Phased migrations | Wave cutovers with testing and support coverage |
| Support & post-migration cleanup | Hyper-care and sign-in reporting |
For a CFO, these deliverables are the control system: one can fund milestones, not ambiguity.
Discovery is the #1 migration bottleneck thus it is recommended you book our “$10K fixed‑price AI‑powered Okta Discovery Assessment” with no hidden fees.
Proof that this approach works in real environments
The global SaaS customer story is compelling because it contains the “messy reality” buyers trust: 156 apps, 66 groups, MFA, and real production constraints. This is the kind of environment where weak discovery burns money.
What Netwoven’s AI Discovery Workbench Agent is
Discovery is where budgets go to die: weeks of manual audits, spreadsheet archaeology, and assumptions that turn into change orders later. Netwoven’s AI Discovery Workbench is an AI based migration planning platform designed by Netwoven to help organizations take control of identity discovery—so you can plan an Okta to Entra ID (Azure AD) migration based on evidence, not guesses.
What it actually does during discovery:
- Tenant analysis: connects to both Okta and Entra environments to provide a unified view of the identity landscape.
- User & group discovery: inventories users, groups, and membership relationships across both platforms.
- Application mapping: maps Okta-integrated apps and assignments and provides compatibility recommendations toward Entra ID equivalents.
- Policy analysis: reviews authentication policies, MFA configurations, and Conditional Access rules to identify gaps and migration risk.
- AI-powered insights (natural language): lets stakeholders ask questions about migration data and get actionable answers.
- Executive-ready outputs: produces exports/reports (Word/Excel/PDF) so finance, security, and IT can align quickly.
Why this matters to CFOs and CIOs?
- For CFOs: it replaces open-ended discovery hours with a bounded assessment and clear artifacts—inventory, gaps, and a plan—so the business case is grounded in reality.
- For CIOs: it exposes hidden dependencies (policies, access paths, user/app relationships) early—before they become incidents or outages during execution.
The Cost of Inaction: The “Identity Tax” you keep paying
When Okta and Entra operate as overlapping identity planes, you pay an identity tax in three ways:
1) License duplication – the obvious one
2) Admin overhead – two policy engines, two troubleshooting paths
3) Security and audit complexity – more drift, more exceptions, more surface area
This is why consolidation is not just a licensing play. It’s an operational efficiency play.
Migration Readiness Scorecard
Use this to evaluate any Okta migration partner.
Discovery readiness (scope control)
- Complete application inventory with owners
- Documented provisioning rules and identity flows
- Clear separation of migration vs optimization
Entra readiness (security control)
- MFA/SSPR posture assessed and remediations identified
- Conditional Access approach defined (parity and rollout)
- Staged rollout strategy
Execution readiness (business continuity)
- Application staging and test migration steps
- Wave plan with cutover and rollback discipline
- Hypercare plan and sign-in reporting