When I am exploring the breadth of SharePoint 2013 PowerShell and would like to dig a little deeper to understand what each of the commands are doing and what set of command are available for given operation or area of SharePoint functionality, or would like to debug some of the run time issues you may incur, I like to explore with the .Net Reflector.
Here I wanted to provide you with some guidance on your way around exploring the SharePoint 2013 PowerShell.
Setup
- First of all, of course you will need to have your SharePoint 2013 On Prem installed and an existence of live farm .
- You could use any commercial available Obfuscator tool. I use Red gate .NET Reflector.
Exploring
- Run the .Net Reflector.
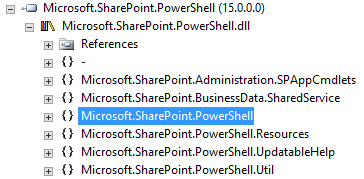
- Locate the Powershell assembly as below. With .Net 4, the assembly location is now located under C:WindowsMicrosoft.NETassembly
- For powershell assembly locate the following folder
C:WindowsMicrosoft.NETassemblyGAC_MSILMicrosoft.SharePoint.PowerShellv4.0_15.0.0.0__71e9bce111e9429cMicrosoft.SharePoint.Powershell.dll
- Once you have loaded the PowerShell assembly, you will see following name spaces
- In order to look up the usual SharePoint Command Lets such as Get/Set/New/Delete/Remove commands look below under the SPCmdlet groups to locate your desired command
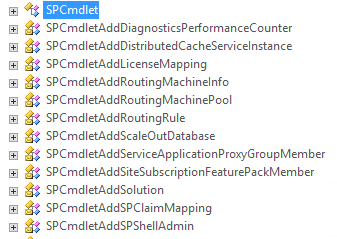
- Lets explore one of the commandlet we all use Add-SPSolution.
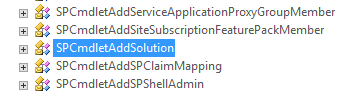
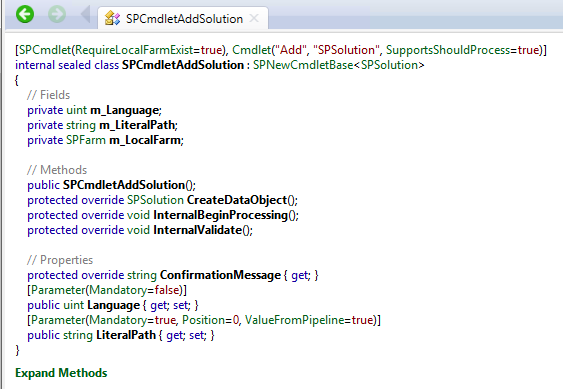
- So locate the SPCmdLetAddSolution as below:
- On the Details pane you should see the method partial details as below
- Now click on Expand Methods to further expand the details of each method. Partial view below:
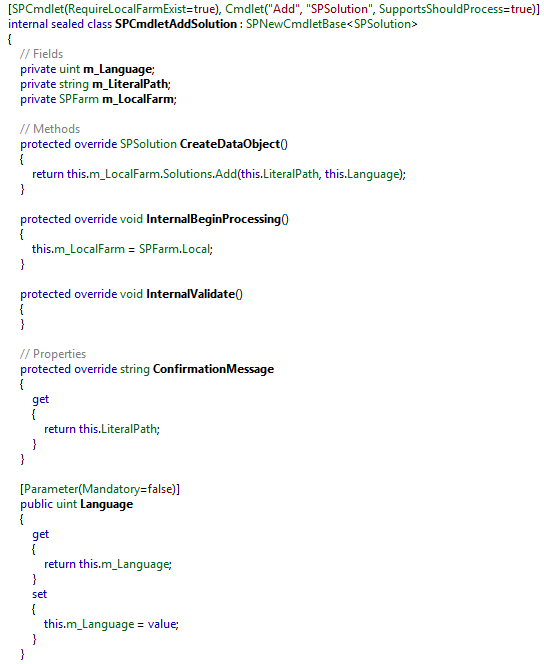
- Here under the SPSolution method you will see that there is call for _LocatFarm object which is based on the SharePoint Object Model.
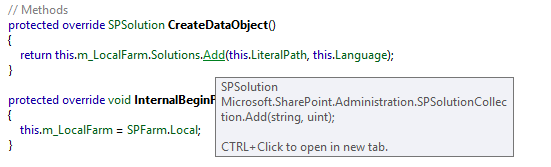
- So let’s click on the add method, and you will see that the call is pointing to the object model, and there you further explore the real call details.
Conclusion
Likewise, being able to explore the specific calls by knowing your API calls, you can further diagnose your Farm Issues, Configuration Issues and Development issues.