Introduction
Identity is no longer an IT line item, it’s a board-level control point that impacts cost, security, and operational velocity.
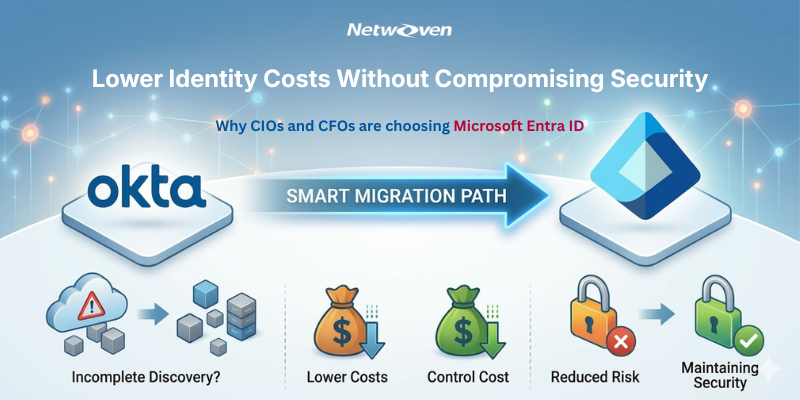
Many organizations find themselves running Okta plus Microsoft Entra ID as environments evolve especially when Microsoft 365 adoption grows and IAM requirements expand across SaaS apps, devices, and users.
But dual-IAM often introduces duplicate spend (overlapping capabilities and licensing), tool sprawl (two policy engines, two admin experiences), and risk seams (inconsistent MFA, conditional access, and governance coverage across apps).
This guide helps you evaluate with clarity by comparing Okta vs Microsoft Entra ID across the areas that usually determine outcomes: SSO, MFA, Identity Governance, Adaptive Access, and CIAM—and how each choice affects security posture, user experience, and total cost of ownership.
We know that Identity and access management is core to any organization, securing productivity in our modern day and age. IAM solutions provide organizations with the ability to authenticate, authorize, and manage the identities and access of their employees, customers, and business partners concerning different applications and devices. IAM solutions also help organizations in the efforts of regulatory compliance and privacy requirements. These are essential to the prevention of data breaches and allow for the highest quality of user experience.
Entra ID and Okta are very strong IAM solutions with varied suites, advantages, and features for different use cases and scenarios. Entra ID is a cloud service that lies within the Microsoft Azure ecosystem and provides critical IAM functionality for Microsoft Cloud services and some third-party applications. On the other hand, Okta is a cloud-based environment that integrates IAM services for customer identity and workforce.
In this blog, a comparison between Okta and Entra ID features is presented as follows:
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Identity Governance and Administration (IGA)
- Adaptive Access Management (AAM)
- Customer Identity and Access Management (CIAM)
We will provide advantages and disadvantages for each solution and an overview of the various recommendations for you to choose the best IAM solution.
Comparison Between Okta and Microsoft Entra ID
| Feature | Okta | Microsoft Entra ID |
|---|---|---|
| Identity Governance and Administration (IGA) | Allows the automated provisioning and de-provisioning of users to applications and directories. Role-based access control is supported, along with self-service requests, approvals, certifications, and reporting. | Entra ID P2 includes native IGA and privileged access controls that often replace third‑party governance tools. It offers: – Entitlement Management – Access Reviews – Privileged Identity Management (PIM) Enables provisioning and de-provisioning of users to Microsoft Cloud services and some external applications. Role-based access control and reporting are supported. |
| Multi-Factor Authentication (MFA) | It offers factors such as SMS, voice calls, email, mobile applications, security questions, biometrics, and hardware tokens. Enables granular policies based on user, group, location, network, device, and application. | It offers deeply enterprise-grade MFA, especially in regulated environments. Microsoft Entra ID (P1/P2) supports: – FIDO2 security keys – Passwordless (Windows Hello for Business) – Certificate-based authentication – Authenticator app (push, number matching) – Risk-based MFA via Identity Protection Allows conditional access policies based on user, group, location, network, device, and application. |
| Single Sign-On (SSO) | Ensures secure entry to all applications using a single set of credentials, irrespective of the application being mobile, cloud, or on-premises. Works with SAML, OpenID Connect, WS-Federation, and others. | Delivers effortless access to Microsoft Cloud services and numerous third-party applications. Works with SAML, OpenID Connect, WS-Federation, and other standards. |
| Adaptive Access Management (AAM) | Employs machine learning and contextual data to detect and respond to anomalous behavior and risky sign-in attempts. Provides customizable risk scoring and granular remediation actions. | This integrates with Azure AD Identity Protection for possible compromise and suspicious activities detection and reaction. Provides pre-configured risk levels and policies. |
| Customer Identity and Access Management (CIAM) | Enables firms to safely manage customer identities and preferences on a large scale. Provides social login, consent management, progressive profiling, and loyalty programs. | Integrates with Microsoft Entra External ID (formerly called as Azure AD B2C) to provide identity and access management for consumer-facing applications. Supports social login, consent management, and custom policies. |
Case Study
A leading SaaS development company smoothly migrates from Okta to Microsoft Entra ID to integrate well with the Microsoft 365 ecosystem and to optimize expenses. Netwoven undertook the project with a comprehensive approach. It assessed the background of the current Okta environment. The target Microsoft Entra ID environment was also examined for best practices around user security, branding, application provisioning, group-based licensing and assignments, application consent, and more.
Advantages and Disadvantages
Okta and Microsoft Entra ID both have their strengths and weaknesses depending on the use case and scenario.
Here are some of the advantages and disadvantages of each solution:
Okta
Advantages
- Delivers a comprehensive and unified suite of IAM services for both workforce and customer identities.
- Accommodates a diverse array of applications, devices, and standards, including cloud, on-premises, and mobile environments.
- Offers flexible and customizable solutions for authentication, authorization, and governance.
- Utilizes machine learning and contextual data to enable adaptive and intelligent access management.
- Improves customer experience and loyalty through features like social login, consent management, progressive profiling, and loyalty programs.
Disadvantages
- Might necessitate additional integration and configuration efforts for certain applications and scenarios.
- Could lead to increased costs and complexity when managing multiple IAM solutions.
- Might not provide the same level of integration and compatibility with Microsoft Cloud services and applications as Entra ID.
Microsoft Entra ID
Advantages
- Provides essential and dependable IAM features for Microsoft Cloud services and some third-party applications.
- Ensures a smooth and uniform sign-in process across Microsoft Cloud services and applications.
- Works well with other Azure offerings like Azure AD Identity Protection, Azure AD B2C, and Azure AD Domain Services.
- Cuts down expenses:
- Elimination of duplicate IAM licenses
- Bundling with M365 E3/E5
- Reduced third-party governance tools
- Simplifies management by using a single IAM solution.
Disadvantages
- Might lack the range of features and adaptability that Okta offers for certain applications and situations.
- Might not work with some applications, devices, and standards unrelated to Microsoft or not based in the cloud.
- Might not give users the same level of personalization and smart features as Okta for authentication, authorization, and governance.
- Might not boost customer satisfaction and retention as much as Okta does with social login, permission management, step-by-step profiling, and loyalty programs.
Recommendations
Choosing the right IAM solution for your company depends on several things, like what your business needs, how much you can spend, what apps and systems you already have, and what you plan to do in the future.
Here is some advice for common situations:
- If you want a full IAM package that works with lots of apps, devices, and standards, and gives you options to customize how people log in, what they can do, and how you manage it all then Okta might be the way to go.
- If you’re after basic trustworthy IAM features that play nice with Microsoft Cloud services and applications, and you want to keep things simple and cost effective by using just one IAM system then Entra ID could be your best bet.
- If you’re after an IAM solution that blends the strengths of different approaches, you might want to think about using Okta and Entra ID together, based on what you need and the situation at hand. As an example, you could use Okta to manage customer identity and access management, while relying on Entra ID to handle workforce identity and access management.

Solution Brief: Okta to Entra ID Migration
As cloud SaaS matured, identity providers like Okta and Microsoft transformed authentication with advanced SSO, lifecycle management, and threat detection. Today, many organizations are shifting from Okta to Entra ID for tighter integration and improved security using tools they already own.
Get the Solution BriefConclusion
It is not about who is better than whom when we compared Okta to Microsoft Entra ID, it’s whether your identity architecture can reduce risk seams, simplify operations, and eliminate duplicated spend without creating friction for users. If your environment is Microsoft 365/Azure–centric and your priority is a single control plane for access policies and governance, consolidating into Microsoft Entra ID is typically the most direct path to standardization and tool rationalization. If your reality is a highly heterogeneous app ecosystem and you need vendor-neutral breadth, mature integrations, and consistent access across thousands of applications, Okta is often the better fit. And if your workforce and customer/partner identity needs are materially different—or you’re transitioning— a hybrid model can be the most pragmatic approach, using each platform where it fits best. If you have more queries, please reach out to us.